Find Useful Mobile Phone Accessories For You
Need to find stowed away possibilities of your cell phone? Then, at that point, cell phone extras can finish the work for you. There are verity of things that can be utilized as embellishments. Regardless of whether you will utilize …
Can’t get new lungs? Try refurbished ones instead.
Spruced up human and animal organs could someday be the solution for people needing transplants.…
Terrible people have learned to exploit the internet. Yasmin Green is fighting back.
The Jigsaw team at Alphabet brings people who were radicalized online back from the brink, one video at a time.…
Residential solar is cheap, but can it get cheaper? Paths to $0.05 per kWh

Tesla smooth black glass solar roof tiles. (credit: Tesla)
The price of solar panels has fallen far and fast. But the Energy Department (DOE) wants to bring those costs down even further, especially for residential homes. After all, studies have
Good news: Chrome debuts automatic blocking of annoying ads

Enlarge (credit: Daniel Oines)
Google developers this week debuted a long-anticipated feature in Chrome that automatically blocks one of the Internet’s biggest annoyances—intrusive ads.
Starting on Thursday, Chrome started filtering ads that fail to meet a set of criteria
How The Drone Industry Evolve In 2018

Drones are a perfect example of how our technology has evolved and will continue to grow in the future. So, what exactly does it offer? For casual users, it is just a fun toy. However, drones have use cases in …
Bitcoin miner in NYC home interfered with T-Mobile network, FCC says
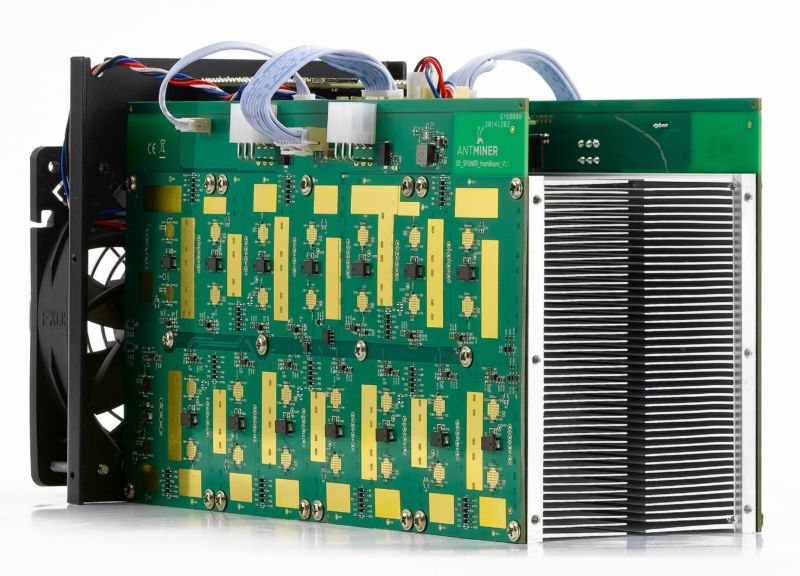
Enlarge / An Antminer S5. (credit: Bitmain)
A New York City resident was ordered to turn off his bitcoin miner after the Federal Communications Commission discovered that it was interfering with T-Mobile’s wireless network.
After receiving a complaint from T-Mobile
How UPS delivers faster using $8 headphones and code that decides when dirty trucks get cleaned
Inside EDGE: the shipping giants’s ambitious, tech-driven bid to keep Amazon and others at bay.…
Raw sockets backdoor gives attackers complete control of some Linux servers

(credit: Jeremy Brooks)
A stealthy backdoor undetected by antimalware providers is giving unknown attackers complete control over at least 100 Linux servers that appear to be used in business production environments, warn researchers.









